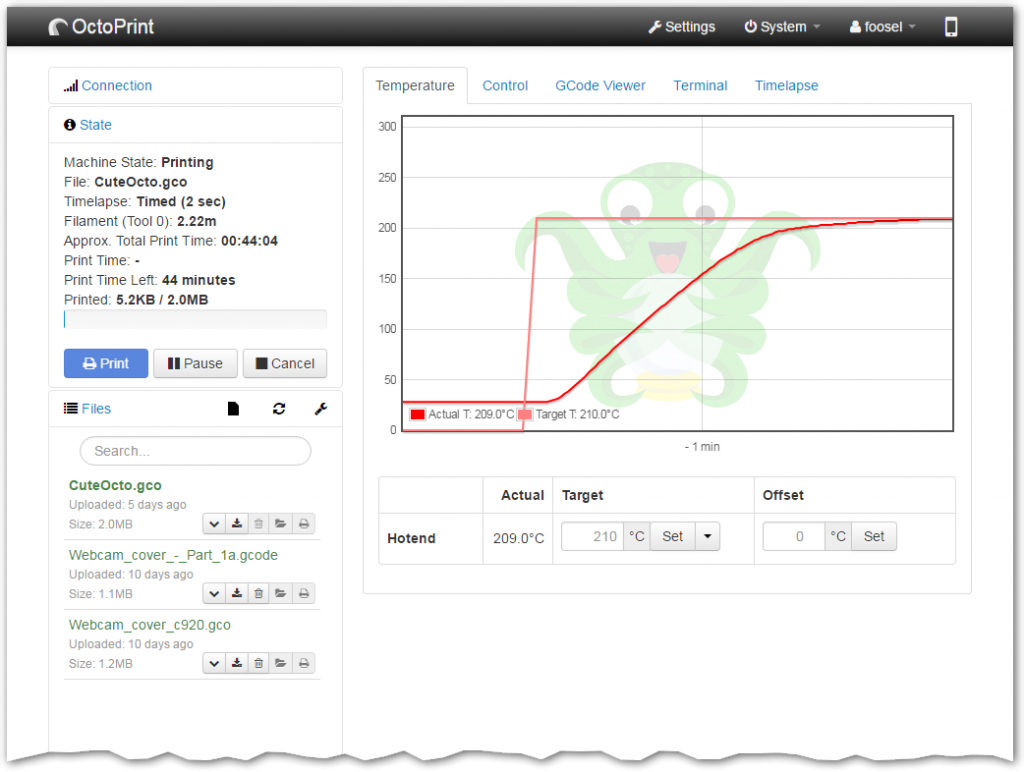
OctoPrint, developers of an open source interface for 3D printers, has issued a reminder to users to configure settings for optimal security.
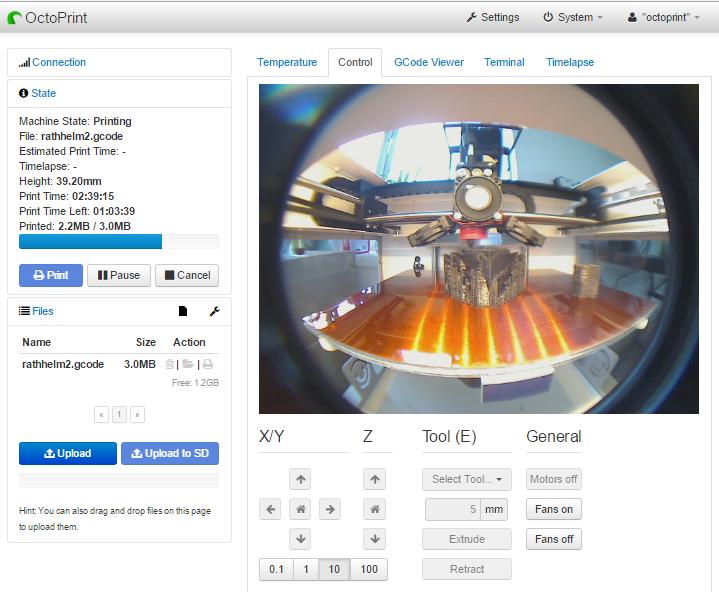
OctoPrint software is widely used by the 3D printing community to control and monitor many aspects of print runs. It is a highly extensible tool created by developer Gina Häußge and made available under an open source license.
Remote access to 3D printers
The reminder follows an article published by the Internet Storm Center (ISC), a group monitoring disruptive or malicious activity and threats to online security. In this article by Xavier Mertens, Senior ISC Handler – Freelance Cyber Security Consultant, a potential attack against an unsecured OctoPrint linked 3D printer is described.
The researchers found that 3,759 3D printers using OctoPrint could be accessed without a requirement for authentication. According to the ISC, if a malicious actor were to access a 3D printer then, “printer owners could face very bad situations.”
These situations include potential leakage of proprietary IP and trade secrets. In a more extreme situation ISC hypothesize that, “what if the attacker downloads a G-code file, alters it and re-upload it. By changing the G-code instructions, you will instruct the device to print the object but the altered one won’t have the same physical capabilities and could be a potential danger once used. Think about 3D-printer guns but also 3D-printed objects used in drones. Drone owners are big fans of self-printed hardware.”
How to secure your 3D printer
Responding to the ISC, OctoPrint has re-iterated the importance of proper configuration. And while the startup wizard for OctoPrint actively warns against allowing unauthenticated access, some users may have disregarded this.
As the OctoPrint blog post states, “While it is possible that a percentage of the instances found are unintentionally exposed, the vast majority is very likely users who have gone out of their way to expose OctoPrint to the public internet for the sake of convenience.”
The ISC article is a useful as it draws attention to a potential issue with OctoPrint users choosing to disable a security function. However, it must be clear that no issues were found when OctoPrint is used in the manner that the developers intend. Indeed the Guide to Safe Remote Access of OctoPrint, provides many pointers on avoiding unnecessary risk and as the video made using OctoLapse below shows, the software has some great functions.
As Gina Häußge writes, security is an important subject, “which I’m starting to sound like a broken record – please heed this warning and invest the time that properly securing internal services needs.”
Read more about Gina Häußge’s thoughts on open source, software development and 3D printing here.
Subscribe now to the 3D Printing Industry newsletter, find us on Facebook and like us on Twitter.
Looking for jobs in 3D printing? Search open opportunities and apply with 3D Printing Jobs. You can also make a profile to advertise your latest vacancies.
Featured image shows the OctoPrint logo.